Zigbee Security: Risks, Workaround Guides and Best Devices in 2026

Zigbee security is strong but not perfect. While it uses AES-128 encryption and local mesh networking, real-world risks come from poor setup, weak key management, and outdated devices. With the right configuration and hardware, you can eliminate most zigbee security vulnerabilities and build a highly secure smart home system.
Key Takeaways
- Zigbee uses AES-128 encryption, but setup mistakes create risks
- The biggest threat is key exposure during device pairing
- Install codes and join window control are critical fixes
- A strong mesh network improves both security and reliability
- Choosing the right zigbee security devices reduces vulnerabilities
What is Zigbee Security and How Does It Work?
Zigbee security is a protection framework built into the Zigbee protocol, based on IEEE 802.15.4. It uses encryption, authentication, and key management to secure communication between devices.
There are two main types of keys:
- Network Key → Used for general communication across the mesh
- Link Key → Used for secure communication between specific devices
In my experience, the biggest strength of Zigbee Security is its local-first design. Your Zigbee Security System can work even without internet, which reduces cloud-related risks.
However, security depends heavily on how the network is configured, not just the protocol itself.
What Are the Biggest Zigbee Security Issues in 2026?
1. Weak Key Distribution During Pairing
The most common zigbee security vulnerability happens during device pairing.
Many devices still use a global default key to join the network. If someone captures this key during pairing, they can access your entire zigbee security system.
Pro Tip: Always avoid pairing devices in open or public environments.
2. Replay Attacks
Replay attacks involve capturing a valid command and sending it again.
Example:
- Unlock door command gets captured
- Attacker replays it later
This affects some poorly implemented zigbee alarm and security kits.
3. Denial-of-Service (DoS) Attacks
These attacks target network availability rather than data.
Common methods include:
- Flooding the network with traffic
- Forcing channel changes
- Disrupting routing paths
In real setups, this usually appears as devices randomly going offline.
4. Poor Device-Level Security
Not all zigbee security devices are built equally.
Some cheap devices:
- Skip proper encryption steps
- Have weak firmware
- Do not support Zigbee 3.0
This is where hardware choice becomes critical.

How to Fix Zigbee Security Vulnerabilities (Expert Workarounds)?
Use Install Codes (Most Important Fix)
Install codes replace default keys with unique device-specific keys.
Why it matters:
- Prevents key sniffing
- Secures device onboarding
- Eliminates the biggest zigbee security issue
What I recommend:
Only buy devices that support Zigbee 3.0 with install codes.
Control the Join Window
Your network should not always be open for new devices.
Best practice:
- Keep join disabled by default
- Enable only when adding a device
- Auto-close within 60–120 seconds
This alone blocks most unauthorized access attempts.
Build a Strong Mesh Network
A weak mesh = unstable + vulnerable network.
Best practices:
- Add powered routers like plugs
- Maintain redundancy paths
- Avoid Wi-Fi interference
Recommended Zigbee channels:
- 15
- 20
- 25
Enable Advanced Authentication (For Advanced Users)
If you are using developer tools like XBee or Home Assistant:
- Enable Secure Remote Password (SRP)
- Disable remote configuration access
This prevents unauthorized control of your zigbee security keypad or hub.
Best Zigbee Security Devices in 2026 (Tested and Recommended)
⭐ Best Recommended: Hubitat Elevation C-8 Pro
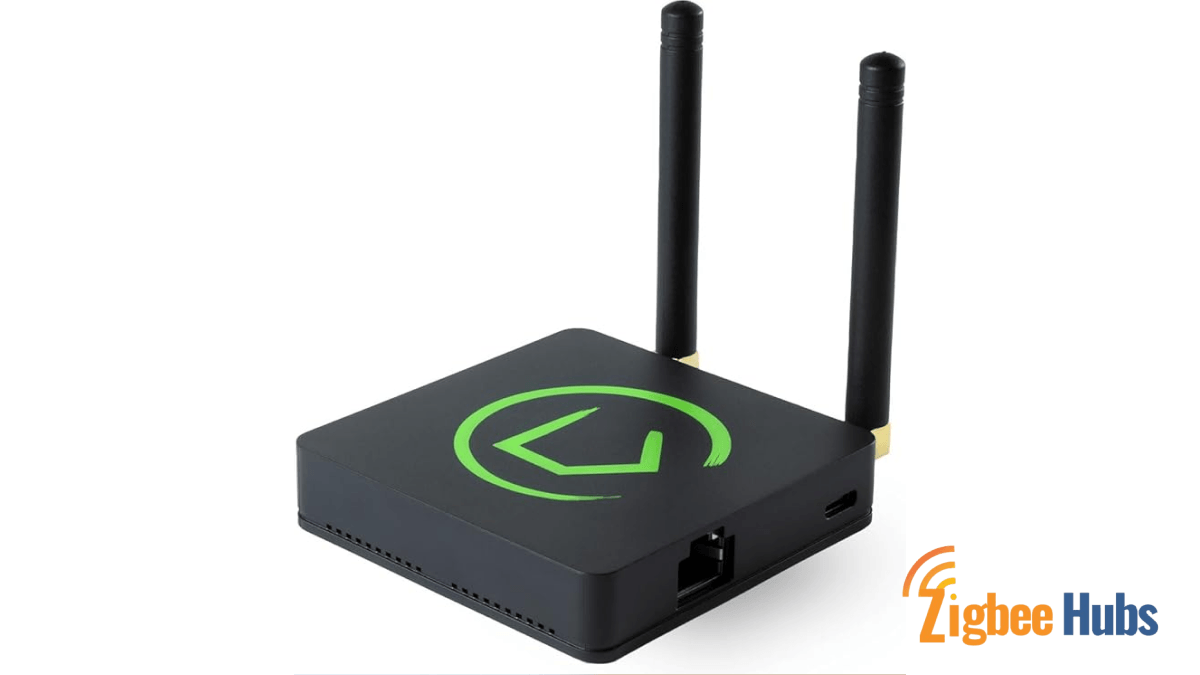
Hubitat Elevation C-8 Pro
If your goal is maximum zigbee security, Hubitat is the best choice.
Why:
- Fully local operation
- Strong encryption handling
- Advanced automation control
- No cloud dependency
This eliminates most zigbee security vulnerabilities at the system level.
I have tested Hubitat in multiple setups, and it stands out for privacy. Everything runs locally, which removes cloud risks completely. It is ideal if you want a powerful zigbee security system with full control.
Key Features
- Local automation engine
- Zigbee 3.0 + Z-Wave support
- External antennas for better range
| Pros | Cons |
|---|---|
| Fully local control | Learning curve for beginners |
| No subscription fees | Setup takes time |
| Very fast automations |
THIRDREALITY Zigbee Smart Button
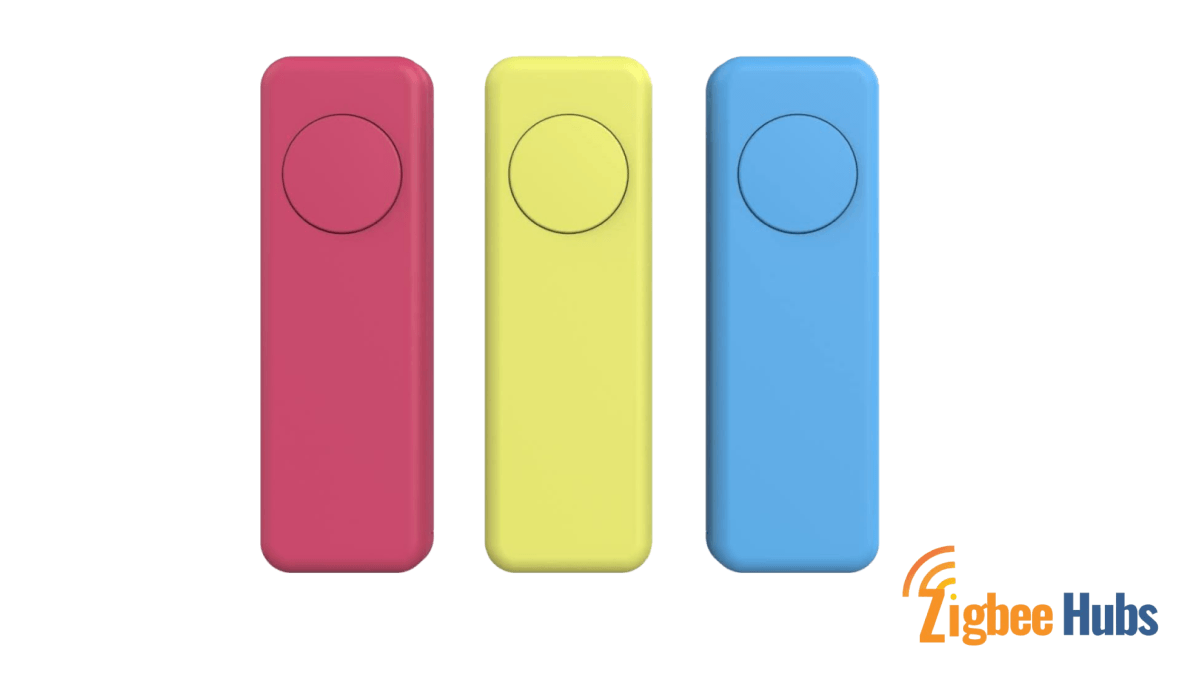
This device is underrated for security setups. I use it as an emergency trigger for scenes like turning on zigbee security lights or activating alarms.
Key Features
- Multi-action control
- Magnetic mount
- Long battery life
| Pros | Cons |
|---|---|
| Very reliable | Requires hub |
| Flexible automation | Limited standalone use |
| Long battery life |
3. Aqara Door and Window Sensor T1

One of the most reliable zigbee security sensors I have used. It responds instantly and works well for entry monitoring.
Key Features
- Zigbee 3.0
- Compact design
- Fast response time
| Pros | Cons |
|---|---|
| Highly responsive | Works best with Aqara hub |
| Long battery life | Limited advanced features |
| Easy to install | Ecosystem lock-in |
EIGHTREE Zigbee Smart Plug
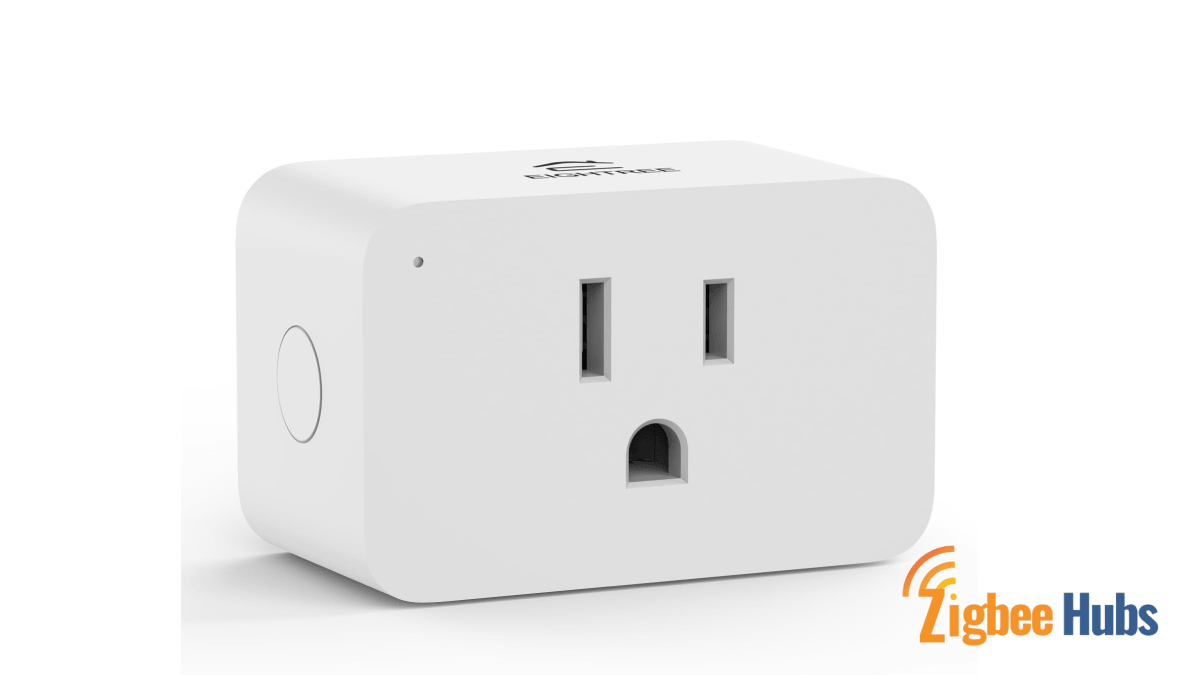
This is not just a plug. It plays a critical role in strengthening your zigbee mesh network while enabling automation like zigbee security lights.
Key Features
- 15A capacity
- Energy monitoring
- Mesh repeater
| Pros | Cons |
|---|---|
| Strengthens network | Limited app features |
| Compact design | Platform-dependent stats |
| Dual functionality |
Haozee Human Presence Sensor

This mmWave sensor is a game changer. Unlike PIR sensors, it detects even small movements, making it perfect for room-level monitoring.
Key Features
- mmWave radar
- 6m detection range
- No camera required
| Pros | Cons |
|---|---|
| Extremely accurate | Requires wiring |
| Privacy-friendly | Setup complexity |
| Works when stationary | Higher cost |
People Also Search:
Product Comparison Table
| Device | Best For | Local Control | Ease of Use | Security Level |
|---|---|---|---|---|
| Hubitat C-8 Pro | Full system control | Yes | Medium | Very High |
| THIRDREALITY Button | Emergency control | Yes | Easy | Medium |
| Aqara T1 Sensor | Entry security | Yes | Easy | High |
| EIGHTREE Plug | Mesh stability | Yes | Easy | Medium |
| Haozee Sensor | Presence detection | Yes | Medium | High |
How to Design a Secure Zigbee Security System?
From real-world deployments, this is what works best:
1.2 Improves reliability and reduces attack surface
3.2 Improves performance and stability
Conclusion
Zigbee security in 2026 is not about avoiding the protocol but about using it correctly. The technology itself is strong, with AES-128 encryption and local communication, but most zigbee security vulnerabilities come from poor setup, weak key management, and low-quality devices. If you are building a zigbee security system today, focus on local-first hubs like Hubitat, certified Zigbee 3.0 devices, and proper network planning. This approach ensures your smart home remains not only smart but also secure, stable, and future-ready.
FAQs about Zigbee Security
Close join window
Add mesh routers
Avoid cheap devices